Cybercriminal's Office365 Scheme Yields Millions, Says FBI
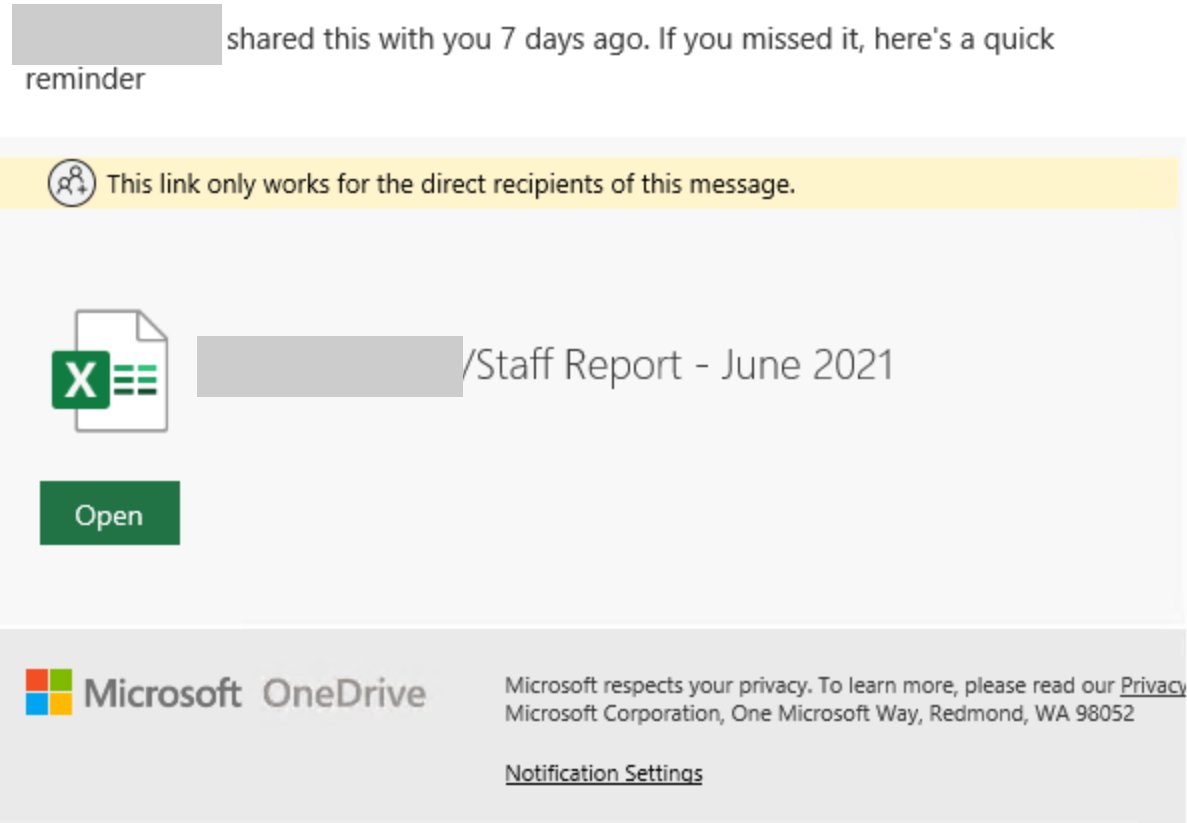
Table of Contents
The FBI's Revelation: How the Office365 Scheme Unfolded
The FBI investigation uncovered a sophisticated Office365 phishing attack that involved multiple stages, ultimately leading to significant financial losses and data breaches. The cybercriminals employed a multi-pronged approach targeting vulnerable businesses. This BEC (Business Email Compromise) attack leveraged several key vulnerabilities and user errors.
- Stage 1: Phishing Emails: The attack began with highly convincing phishing emails designed to mimic legitimate communications from trusted sources. These emails often contained malicious links or attachments.
- Stage 2: Credential Harvesting: Once a user clicked a malicious link or opened an infected attachment, malware was deployed to harvest login credentials, specifically targeting Office365 accounts.
- Stage 3: Account Takeover: With access to valid credentials, the cybercriminals gained unauthorized access to the victim's Office365 accounts.
- Stage 4: Data Exfiltration: After gaining access, the attackers exfiltrated sensitive data, including financial records, customer information, and intellectual property.
- Stage 5: Ransomware Deployment (in some cases): In certain instances, the attackers deployed ransomware, encrypting critical data and demanding a ransom for its release.
The scale of the operation was significant, impacting numerous businesses across various industries. While precise figures on the number of victims remain undisclosed, the FBI confirmed millions of dollars in losses. This highlights the devastating financial impact of successful Office365 phishing attacks and data exfiltration techniques. The use of ransomware deployment further amplified the losses for some victims.
Vulnerabilities Exploited in the Office365 Attack
The success of this Office365 phishing attack relied on a combination of technical vulnerabilities and human error. The cybercriminals exploited several weaknesses:
- Weak Password Security: Many victims used easily guessable or reused passwords, making their accounts vulnerable to brute-force attacks or credential stuffing.
- Phishing Email Vulnerabilities: The attackers crafted highly sophisticated phishing emails that bypassed basic email filtering systems. The emails cleverly mimicked legitimate communications, exploiting trust and urgency to manipulate recipients.
- Social Engineering Techniques: The cybercriminals used social engineering tactics to manipulate users into revealing sensitive information or clicking malicious links. This included creating a sense of urgency or using authority figures as part of their deception.
- Office365 Security Flaws (in some cases): While Office365 offers robust security features, some victims may have had outdated security settings or neglected to implement crucial security measures, leaving them vulnerable.
The Role of Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) is crucial in preventing Office365 security breaches. MFA adds an extra layer of security by requiring users to provide multiple forms of authentication, such as a password and a one-time code from a mobile app or email. Even if an attacker obtains a password, they still need access to the second factor to gain entry. Different types of MFA include:
- Two-Factor Authentication (2FA): The most common type, requiring a password and a second verification method.
- Time-Based One-Time Passwords (TOTP): Uses an authenticator app to generate a time-sensitive code.
- Hardware Security Keys: Physical devices that provide a highly secure authentication method.
- Biometric Authentication: Uses fingerprints or facial recognition for verification.
Implementing MFA is a fundamental step in bolstering Office365 security and mitigating the risk of successful account takeovers. Consider using a password manager to generate and securely store strong, unique passwords for all your accounts.
Protecting Your Business from Similar Office365 Attacks
Protecting your business from similar Office365 attacks requires a multi-layered approach:
- Regular Security Audits: Conduct regular security audits to identify and address vulnerabilities in your Office365 environment.
- Employee Training Programs: Invest in comprehensive cybersecurity awareness training programs to educate employees about phishing scams, social engineering tactics, and safe online practices.
- Strong Password Policies: Enforce strong password policies, including password complexity requirements, regular password changes, and password management tools.
- Advanced Threat Protection: Implement advanced threat protection solutions to detect and block malicious emails and attachments before they reach users' inboxes. This includes email filtering and intrusion detection systems.
- Multi-Factor Authentication (MFA): Enable MFA for all Office365 accounts to add an extra layer of security.
The Long-Term Implications and Future of Office365 Security
The FBI's revelation highlights the evolving tactics of cybercriminals and the need for continuous adaptation of security strategies. The long-term implications include:
- Evolving Cyber Threats: Cybercriminals constantly develop new techniques to bypass security measures. Businesses must stay informed about emerging threats and adapt their security protocols accordingly.
- Cybersecurity Trends: The increasing reliance on cloud services necessitates a proactive approach to cybersecurity. Businesses must invest in advanced security solutions and stay up-to-date on the latest cybersecurity trends.
- Proactive Security Measures: A reactive approach is no longer sufficient. Businesses need to implement proactive security measures, such as regular vulnerability assessments and penetration testing, to identify and mitigate potential threats before they can be exploited.
- Advanced Persistent Threats (APTs): Businesses must be prepared to defend against APTs, which are sophisticated, long-term attacks designed to infiltrate systems and steal sensitive data over an extended period.
Conclusion:
The FBI's revelation of this multi-million dollar Office365 scheme serves as a stark reminder of the ever-present threat of cybercrime. Businesses must proactively strengthen their Office365 security measures to protect themselves from similar attacks. Ignoring these threats can lead to significant financial losses, reputational damage, and legal repercussions. Don't become another victim. Implement robust security measures to protect your organization from Office365 breaches. Learn more about advanced security solutions and best practices to safeguard your business against sophisticated cyberattacks. Invest in your Office365 security today!
Featured Posts
-
 Alex Palous Pole Position Highlights Andrettis Indy 500 Difficulties
May 11, 2025
Alex Palous Pole Position Highlights Andrettis Indy 500 Difficulties
May 11, 2025 -
 Early Season Mlb Powerhouse Jazz Chisholm Jr S Numbers Compared To Aaron Judges
May 11, 2025
Early Season Mlb Powerhouse Jazz Chisholm Jr S Numbers Compared To Aaron Judges
May 11, 2025 -
 Yankees Diamondbacks Injury Update April 1st 3rd Games
May 11, 2025
Yankees Diamondbacks Injury Update April 1st 3rd Games
May 11, 2025 -
 Facing Tik Tok Instagram Ceos Testimony On Platform Growth
May 11, 2025
Facing Tik Tok Instagram Ceos Testimony On Platform Growth
May 11, 2025 -
 Office365 Breaches Net Millions For Cybercriminal Authorities Report
May 11, 2025
Office365 Breaches Net Millions For Cybercriminal Authorities Report
May 11, 2025
Latest Posts
-
 The Hope For Happy Gilmore 2 A New Sandler Classic
May 11, 2025
The Hope For Happy Gilmore 2 A New Sandler Classic
May 11, 2025 -
 A Happy Gilmore Sequel Sandlers Chance For A Hilarious Return
May 11, 2025
A Happy Gilmore Sequel Sandlers Chance For A Hilarious Return
May 11, 2025 -
 Happy Gilmore 2 Sandlers Return To Comedy Gold
May 11, 2025
Happy Gilmore 2 Sandlers Return To Comedy Gold
May 11, 2025 -
 Examining Adam Sandlers Role In A Divided America
May 11, 2025
Examining Adam Sandlers Role In A Divided America
May 11, 2025 -
 Adam Sandlers Hidden Easter Eggs A Complete Guide
May 11, 2025
Adam Sandlers Hidden Easter Eggs A Complete Guide
May 11, 2025
